Download catalogue of technologies
Protosphere: a network traffic analyzer
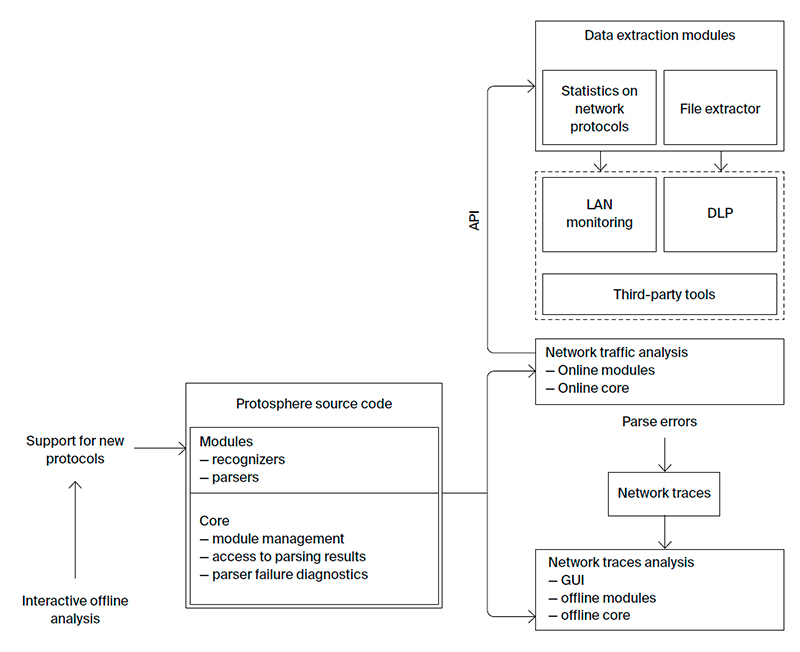
Protosphere is a system of deep packet inspection (DPI). It can serve as a part of intrusion and information leak protection systems. Protosphere detects inconsistencies between a protocol specification and the actual traffic. It allows you to add support quickly for new protocols (either open or closed) due to the flexibility of its internal representation.
Features and advantages
Protosphere is an innovative system based on the innovative research in the area of network traffic analysis. It combines the key features of similar tools (e.g. Wireshark, Microsoft Message Analyzer) with a universal data representation model that enables rapid expansion of analysis capabilities.
Protosphere provides:
- Advanced system core:
- universal data representation model used when parsing network traffic;
- processing of corrupted, reordered or duplicated packets, as well as handling of packet loss and processing of asymmetric traffic;
- compressed/encrypted data analysis;
- support for tunnels of arbitrary configuration;
- support for network flows causality.
- Support for all stages of network trace analysis (each stage has a visualization component that are synchronized between stages):
- network connections localization in the network interaction graph and the network flow tree;
- detailed view of the selected connections in the timeline diagram;
- interactive visualization of the parsed network packets in the stream tree;
- detection of discrepancies between a protocol implementation and the actual traffic in the diagnostic log;
- arbitrary OSI-layer data extraction and analysis (L7+).
- Easy support for new protocols:
- access to parsing results via API;
- localize parsing errors;
- debugging the module being developed on real-time traffic and network traces.
- Support for both online and offline analysis modes.
- Advanced GUI provides choice of the most convenient way to present the analysis results.
- Universal data representation model to accelerate customization:
- support for new protocols;
- extract data in a desired format;
- configuring the analysis results format.
- Adjustment to network bandwidth and available computational resources to find a balance between accuracy of the analysis and the resources consumed.
Who is Protosphere target audience?
Supported platforms and architectures
Architecture: Intel x86-64.
Platforms: Windows and Linux-based OSes.
Protosphere Workflow
Developer/Participant
Back to the list of technologies of ISP RAS 


