Download catalogue of technologies
Svace static analyzer
Svace is an essential tool of the secure software development life cycle, the main static analyzer that is used in Samsung Corp. It detects more than 50 critical error types as well as hundreds of coding issues. Svace supports C, C++, C#, Java, Kotlin, and Go. Svace is included in the Unified Register of Russian Programs (No.4047).
Features and advantages
Svace is an innovative technology based on years of research that constantly evolves for customer’s needs. It combines the key qualities of foreign competitors (Synopsis Coverity Static Analysis, Perforce Klocwork Static Code Analysis, Fortify Static Code Analyzer) with the unique open industrial compilers usage to provide the maximal support level for new programming language standards.
Svace provides:
- High-quality deep analysis:
- accurate representation of the source code (due to integration with any build system);
- full path coverage taking into account function calling contexts when searching for complex defects;
- high percentage of true positives (60-90%).
- Scalability and high speed:
- parallel analysis using all available processor cores;
- ability to analyze software with the code size of tens of millions of lines (analysis of the Tizen 6.5 mobile OS having 44 million lines of code takes 7-8 hours);
- supporting incremental system analysis in addition to the full analysis mode (performs a quick re-analysis of the recently changed source files).
- Convenient warnings viewing interface:
- detailed error description with code navigation;
- review interface for marking true and false positives;
- analysis results migration between runs with hiding any issues previously marked as false positives.
- Accelerated customization (configuring existing detectors as well as writing individual ones available exclusively to this customer; creating tailored user interfaces).
- Ultra fast adaptation to new environments and tools (adding new compilers within 1-2 weeks, in complex cases up to 2 months).
- Full compatibility with regulatory documents and requirements of regulators (FSTEC of the Russian Federation).
- Can be used for adhering to the GOST R 56939-2016 requirements and to the requirements of the FSTEC regulation document mandating software vulnerability detection process (when certifying software within Russia).
What is Svace target audience?
- Companies aimed at software development with a special focus on high reliability and security.
- Companies that need to certify the developed software.
- Certification laboratories.
Svace deployment stories
Svace is the main static analyzer used in Samsung Corp. since 2015. It is used to check the company’s own software based on Android OS as well as the Tizen OS source code. Tizen is used in smartphones, infotainment systems and Samsung home appliances. Since 2017, Svace checks all changes submitted for review and inclusion in the Tizen OS.
Within Russia, Svace is deployed in more than 40 companies and certification labs, including RusBITech, Kaspersky, Postgres Professional, Security Code, and Swemel.
Supported platforms and architectures
- Host platforms for the analyzer: Linux kernel based OS (version 3.13 and later), Windows 7 SP1 and later, including WSL 1 and 2, macOS on x86-64 (starting from 10.12 Sierra); x86-64 and ARM64/Linux architectures; x86 architecture for build capture.
- Target architectures of the analyzed code: Intel x86/x86-64, ARM/ARM64, MIPS/MIPS64, Power PC/Power PC 64, RISC-V 32/64, SPARC/SPARC64, Hexagon (AEON, TriCore, HIDSP, OpenRISC targets of the GCC compiler are partially supported).
Supported Compilers
- For С/С++ (up to C++17): GCC (GNU Compiler Collection), Clang (LLVM compiler), Microsoft Visual C++ Compiler, RealView/ARM Compilation Tools (ARMCC), Intel C++ Compiler, Wind River Diab Compiler, NEC/Renesas CA850, CC78K0(R) C Compilers, C/C++ Compiler for the Renesas M16C Series and R8C Family, Panasonic MN10300 Series C Compiler, C compiler for Toshiba TLCS-870 and T900 Family, Samsung CalmSHINE16 Compilation Tools, Texas Instruments TMS320C6* Optimizing Compiler.
- For С# (up to C# 9): Roslyn, Mono.
- For Java (up to Java 11): OpenJDK Javac Compiler, Eclipse Java compiler.
- For Kotlin: Kotlin 1.5.
- For Go: Go 1.15.
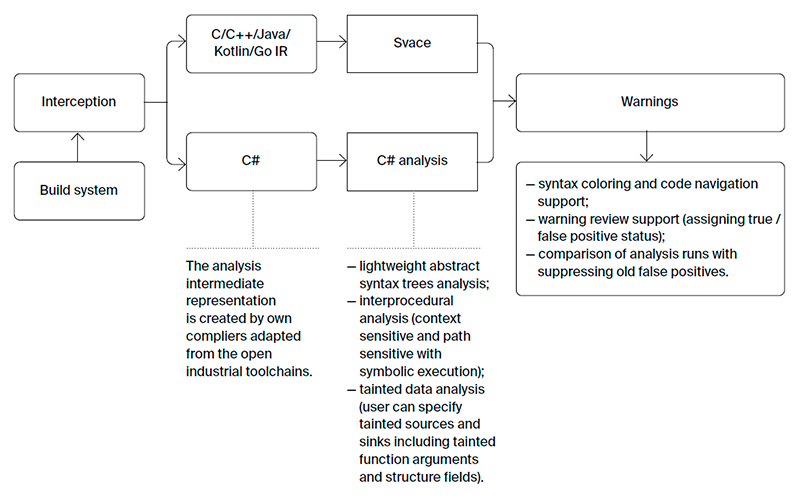
Svace Architecture
Developer/Participant
Back to the list of technologies of ISP RAS 


