Download catalogue of technologies
ISP RAS software analysis platform based on QEMU
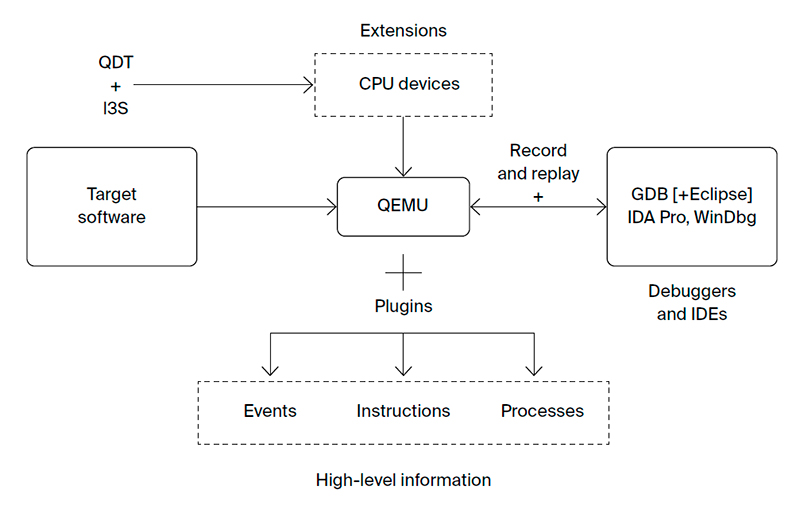
ISP RAS Foundation Platform for creating program analysis systems is built on top of open source QEMU emulator. This framework is essential for organizing cross platform development. It supports reverse debugging and introspection features, as well as full system emulation mode for debugging low-level software.
Features and advantages
QEMU supports emulation of more than 10 instruction set architectures (i386 and x86-64, ARM and Thumb, MIPS, PowerPC, etc.). It implements guest debugging via GDB Remote Serial Protocol and is compatible with IDA Pro, GDB, and various IDEs. QEMU supports full system emulation mode that allows debugging low-level software such as a bootloader and an OS kernel. The QEMU source code is regularly checked by static code analysis tools, including Coverity and Svace. Thus performing malware analysis with QEMU is more secure. QEMU with reverse debugging and introspection support is available on the ISPRAS GitHub page: https://github.com/ispras/swat. The developed QEMU automatization tools are available at https://github.com/ispras/qdt, https://github.com/ispras/i3s.
ISP RAS QEMU Foundation Platform provides:
- A record and replay mechanism for a virtual machine:
- The same VM execution is replayed every time, deterministically. All external events are recorded and replayed by the emulator. It makes finding bugs in multi-threaded applications (race conditions, deadlocks) easier;
- GDB-compatible reverse debugging is implemented based on the record and replay mechanism. The debugging is performed by restoring previous VM snapshots and searching for the previous breakpoint stop or the previous instruction;
- The minimum required information is recorded. This allows recording longer for debugging rarely occurring errors;
- Low performance overhead caused by recording. This enables analysis of software that requires interacting with an uncontrolled external environment in real time.
- VM introspection solution (getting high-level information regarding guest OS work) without any guest OS kernel modifications or installing monitors:
- Getting the list of executed system calls, accesses to named functions in shared libraries, the list of running processes, the list of open files and loaded modules;
- Supports all Linux-based virtual machine images as well as embedded software images for various devices;
- WinDbg server support in QEMU that allows showing guest software information in terms of Windows kernel abstractions. There is no need to enable the OS debugging mode in the guest OS.
- Speeding up QEMU development:
- Faster development of dynamic analysis tools that can analyze binary code for specific hardware;
- Automated support for new processor architectures using a machine instruction decoder generator and a C-like language for describing machine instructions semantics;
- An automatic tool for preliminary virtual machine testing. The tool only requires GNU Binutils and a C compiler;
- A tool for automating QEMU virtual devices development;
- VM generation tool in the form of QEMU module source code. The tool can create VMs from both existing devices and new devices out of Python description. The tool provides GUI for sketching the virtual machine;
- A Python API for an automated debugging via GDB Remote Serial Protocol. It is used to debug QEMU, the guest OS, or both at the same time.
- Convenience and user experience:
- Easy QEMU extension due to open source code and own ISPRAS toolkit for speeding up development;
- Binary code analysis without any guest OS modifications;
- VM introspection mechanism that can be extended using plugins;
- A convenient API for developing own introspection plugins;
- Can be easily adapted for specific use cases;
- Support for latest QEMU versions that have support for newest peripherals and CPUs.
Who is ISP RAS Foundation Platform target audience?
- Bootloader, driver, OS and other system software developers.
- DevOps teams for software bugs reproduction, cross-platform development, and scalable cloud testing.
- Programmers analyzing potential malware.
- Software certification engineers.
Supported guest platforms
Emulation of the following ISAs: i386, x86-64, ARM, MIPS, PowerPC, and others.
Guest systems supported by the introspection mechanism: Windows XP (x86), Windows 10 (x86-64), Linux 2.x-5.x (x86, x86-64, ARM, AArch64).
ISP RAS QEMU deployment stories
The QEMU community has accepted ISP RAS patches for the record and replay mechanism and added them to the open source QEMU version 3.1.
Workflow
Developer/Participant
Back to the list of technologies of ISP RAS 


